DoD’s New Cybersecurity Registration
If you’ve never heard of CMMC (Cybersecurity Maturity Model Certification) you are certainly not alone. It is, however, something you should be aware of should you wish to be a part of any Department of Defense (DoD) contracts. The CMMC is the DoD’s new cybersecurity framework, and the final stages for its initial rollout are underway.
Brief Overview
It’s no secret that the theft of intellectual property and sensitive data costs billions and is a threat to industry and defense. This threat is by no means limited to classified information. The loss of intellectual property and certain unclassified information from the DoD supply chain can thwart U.S. technical advantages and innovation, as well as significantly increase the risk to national security. To combat this, the Office of the Under Secretary of Defense for Acquisition and Sustainment, in conjunction with DoD stakeholders have developed the new CMMC certification as a means to protect this information from a range of cyber threats.
Quick History
To help understand why and how the new certification has been established, Nicholas McBride, Cybersecurity Consultant at Ecuron, provided some history. “Currently, any prime or subcontractor who does business with the DoD, and handles Controlled Unclassified Information, should be self-certified to the NIST 800 171,” he began. “But the problem with self-certification is, people aren’t always as secure as they say they are.” Realizing this shortcoming, the DoD decided they needed a more codified and robust framework requiring third-party assessment.
One of main problems with the NIST standard is it allows for a POA&M (plan of action and management). “This means that if you don’t have a specified control in place, but you have a plan to put it in place over the next year or two, you are compliant,” Nicholas explained. “Whereas, with the CMMC, there will be no POA&M as you are either compliant, or you’re not. So in this regard, it is much more strict for anybody engaging in DoD work.”
Defining the Framework
Before we explore the specifics of the framework and the various levels, it’s a good idea to define three key terms, as they are important in determining what level, if any, of compliance you will need.
- Federal Contract Information (FCI) – FCI is information provided by or generated for the Government under contract not intended for public release.
- Controlled Unclassified Information (CUI) – CUI is information that requires safeguarding or dissemination controls pursuant to and consistent with laws, regulations, and government-wide policies, excluding information that is classified.
- Commercial Off The Shelf (COTS) – COTS products are sold on the public market without any modification.
The CMMC model measures cybersecurity maturity with five levels. Each of these levels, in turn, consists of a set of processes and practices which are characterized in Figure 1. In order for an organization to achieve a specific CMMC level, it must also demonstrate achievement of the preceding lower levels.

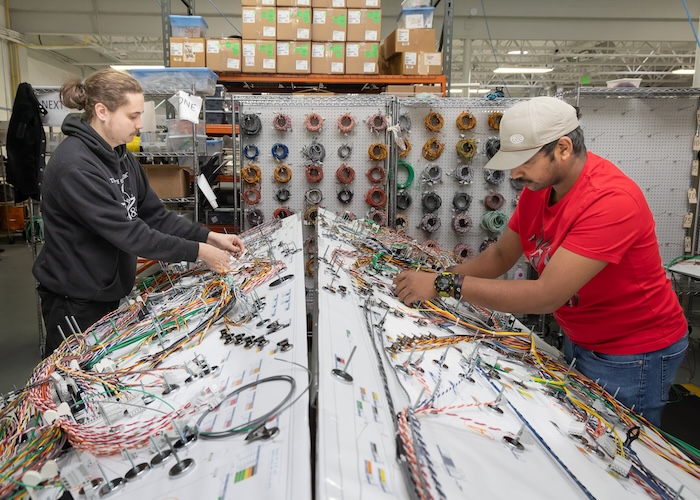
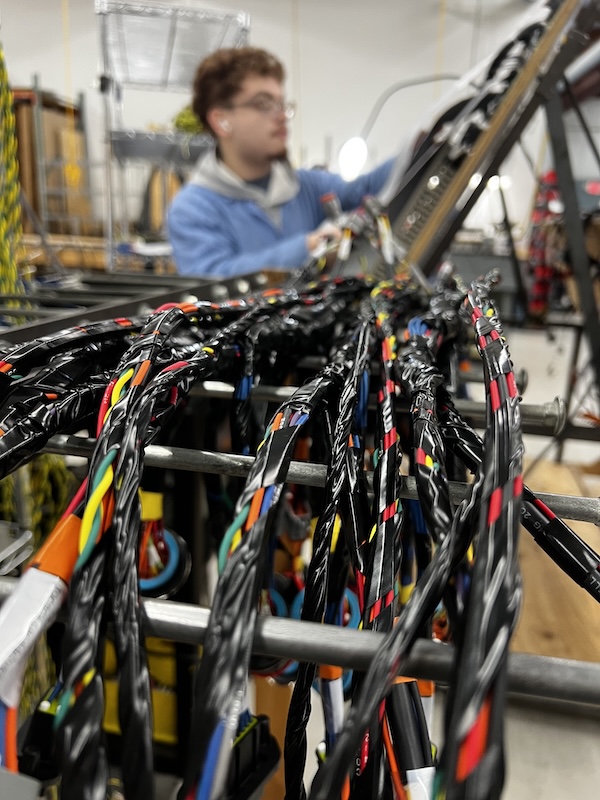
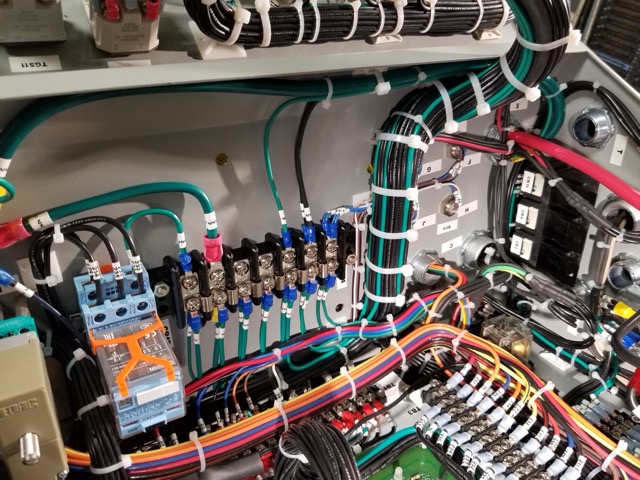
Anybody who handles FCI through the supply chain needs to meet the minimum requirements for Level I. Anybody handling CUI needs to meet Level III minimum requirements. Those who sell COTS products do not need CMMC at all. “So, really, it’s whether or not you handle FCI or CUI that will determine if you need Level I or III,” Nicholas detailed. “The Wire Harness industry represents a very important niche to the defense industrial base ecosystem, and those products could possibly fall under CUI and require a Level III requirement.”
If you are only handling FCI and CUI, you do not need to proceed to any additional levels in the framework to be CMMC registered. Levels IV and V are additional levels for contracts that will require more in-depth protections from Advanced Persistent Threats (APTs). “At this point I would imagine levels IV and V will be for companies who handle extremely sensitive information that is not classified,” Nicholas instructed. “The only companies I’ve talked to so far who need a Level IV or V are aerospace prime contractors with a focus on the Air Force and NASA.”
Even though a wire harness could be used in a highly classified missile system, for example, Nicholas thinks it’s unlikely those designs would extend beyond the CUI Level III. “I do understand wiring harnesses are used in advanced systems, but I imagine that Level III would be the highest level that most of your readers will need. That said, there could be changes down the road, so it’s wise for any subcontractor to ask their prime if they expect they will need a Level IV or V for future contracts.”
Rollout
The DoD is expected to implement the CMMC framework throughout its supply chain over the next several years. By 2026, every contract ordered by the DoD will have the CMMC requirement. Nicholas advised the rollout will be incremental. “Starting in 2021, 15 DoD contracts will have the CMMC requirement. That includes the prime contractors, all the way down to subcontractors, and we estimate that will affect roughly 1000 businesses,” he advised. The DoD will add about 70 additional contracts requiring CMMC in 2022, and 400 in 2023. They will follow that trajectory through full implementation in 2026.
Where to Start
The interim rule on the CMMC has been published and is currently at the end of the 60-day public comment period. Since this could potentially affect harness suppliers in the very near future, Nicholas outlined a great strategy for preparation. “The first step would be to identify whether they will need a Level I or III on the cyber security maturity model (Level II being a transition step to Level III). Should they wish to proceed on their own, they would need to chronicle what cybersecurity safeguards are already in place, and implement those that are missing.”
Nicholas suggested this might be a good time to bring in a consultant such as Ecuron. “We work well beyond a coaching capacity,” he outlined. “We would be writing all of the Level III documents required and directing the implementation of controls.” Ecuron doesn’t do the actual certification, as he indicated that would be a conflict of interest. A full list of third party certifies should be available on the CMMCab.org website by Q1 of 2021.
The next step, whether using a consultant or going it alone, would be to begin fulfilling the Level I requirements. That can be done by referring to the Federal Acquisition Regulation (search FAR 52.204-21). “There are 17 practices listed there,” Nicholas noted, “and basically, if they think they need a Level I, those practices will get them there.”
Should a company determine they will need to meet a Level III requirement, they should be referring to the document NIST SP 800-171, as 80-90% of the Level III CMMC requirement is taken directly from this publication. The additional 10-20% are controls to cover shortcomings the CMMC Advisory Board and DoD have identified with the NIST guidelines. “So, for any organization who wishes to jumpstart the process to Level III compliancy, the best thing to do is refer to the FAR practices and NIST requirements,” Nicholas advised.
“The thing to remember in all of this is there’s no telling which contracts the DoD will pick during the rollout period,” he warned. “A harness manufacturer could find themselves losing out on business that trickles down from one of those bids.” Thus, harness manufacturers doing defense work should focus on the CMMC as it will quickly become the gold standard for demonstrating security. It’s best to get on the train now and set up a clear implementation path.
About Ecuron
Ecuron is a boutique cybersecurity consulting company that specializes in preparing companies to face cyber threats. Their mission is to create a partnership with you, securing your data and protecting your organization every step of the way. For help developing and implementing an information and cybersecurity strategy for your organization and for more information visit https://www.ecuron.com